 For years, cyber insurance was sold to small and mid-sized businesses as a backstop that would take the sting out of a hack. In the beginning, that is what happened. But the landscape is changing fast.
For years, cyber insurance was sold to small and mid-sized businesses as a backstop that would take the sting out of a hack. In the beginning, that is what happened. But the landscape is changing fast.
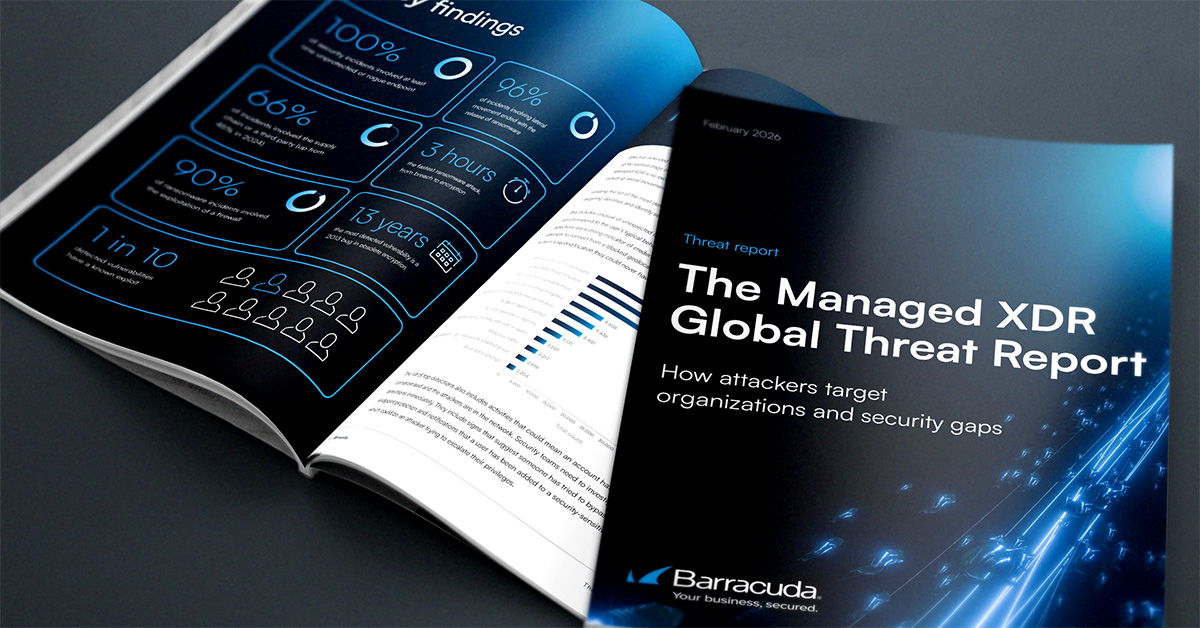
More than 40 percent of businesses that filed cyber insurance claims in 2024 received no payout, according to industry data cited by Fitch Ratings. Premiums are also rising, and Deloitte’s Global Insurance Outlook found that the most common reason for denial was a failure to maintain the security controls businesses attested to on their applications. The gap between client expectations and insurer payouts often leaves MSPs in the middle. If you’ve ever wondered what a rope in a tug‑of‑war feels like, an MSP can tell you.
Why self‑attestation no longer works
Stanislav Kazanov, who leads cybersecurity efforts at Innowise, said the days of taking a client’s word for it are over. “In the past, a client would complete an insurance form, answer ‘yes’ when asked about MFA, and be issued a policy,” Kazanov said. “However, today if there’s any type of breach through a service account that was forgotten about and used by an employee, or through a legacy VPN that wasn’t required to have MFA implemented, the insurance company will deny the claim because the client did not accurately represent what measures were in place for their security posture.”
He added that clients will frequently file lawsuits against their MSPs for failing to provide a secure environment, significantly raising the stakes.
The takeaway, Kazanov said, is that underwriters no longer trust self‑attestation. They now require continuous telemetry data and proof that security controls are enforced across the entire estate—not just 95 percent of it.
What underwriters are actually grading in 2026
Rather than underwriting general IT environments, Kazanov said insurers are now underwriting specific security architectures. To trigger coverage, customers must demonstrate that certain safeguards are fully implemented. At the same time, Barracuda Networks offers a range of products and solutions designed to help businesses remain compliant.
According to Kazanov, some of the must‑haves include:
Phishing‑resistant identity. Standard SMS or app‑based MFA is no longer enough to qualify for premium discounts. Underwriters expect biometric authentication, hardware‑based FIDO2 security keys, or tightly enforced Conditional Access policies.
Tested, immutable backup. It is no longer sufficient for a business to claim its data is backed up. Backups must be cryptographically locked and air‑gapped. MSPs must conduct documented quarterly tabletop exercises that prove recovery within a defined Recovery Time Objective.
EDR with 24/7 SOC coverage. Traditional antivirus tools no longer satisfy coverage requirements. Insurers increasingly require EDR or XDR solutions that are monitored around the clock by human analysts who can autonomously isolate compromised endpoints at any time.
How MSPs can close the gaps—and protect themselves
Kazanov said MSPs must stop positioning themselves solely as IT support and instead act as true risk partners. That means aligning service offerings with the control requirements of leading cyber insurance carriers. It also means changing the framing of those services to clients.
“You need to purchase this specific set of security services, or you will mathematically fail your insurance industry’s audit next month,” Kazanov said, describing how that conversation should sound. When clients refuse immutable backups or segmentation, MSPs can’t simply move on. Kazanov said MSPs should instead require clients to sign formal risk acceptance waivers. This allows them to acknowledge that refusing these controls could invalidate their cyber insurance and that the MSP will be held harmless if a claim is later denied.
“MSPs have always been the bridge between technical reality and financial liability,” Kazanov said. “You can transform yourself from selling IT to selling financial survivability by aligning your services with the exact requirements of the underwriters who write the client’s policy.”
The risks MSPs often underestimate
Jordan Blake, Director of Communications and Operations at Shoreline Public Adjusters, said his team sees the consequences of misalignment firsthand. Especially how claim denials rarely hinge on the incident itself. Shoreline Public Adjusters, LLC represents policyholders, not insurers, in navigating insurance claims, including cyber losses.
“Most cyber claims we work trace back to a misalignment between what was stated at binding and what actually existed at the time of loss,” Blake said. “Carriers are rescinding coverage or denying claims due to material misrepresentation. This could include stating ‘MFA on all remote access’ when MFA was missing on a legacy VPN, or claiming a ‘tested incident response plan’ when the plan was just a Word document no one had opened.”
While the business owner signs the insurance application, Blake noted that the MSP understands what security controls are in place. When those attestations are inaccurate, MSPs are often named in downstream errors and omissions claims.
Blake added that MSPs winning renewal conversations in 2026 are producing attestation evidence before brokers ask. They deliver annual documentation packets mapped directly to common cyber insurance application questions.
The underappreciated denial: social engineering sublimits
Blake also highlighted a denial category that catches many businesses by surprise: social engineering sublimits.
“Many denials we’ve seen this year weren’t full denials—they were sublimit surprises,” Blake said, pointing to scenarios where a business wires $400,000 to a fraudster only to discover afterward that coverage is capped at $100,000 or requires callback verification procedures that were never followed.
MSPs, he said, can often prevent these outcomes by reviewing social engineering and fraudulent transfer endorsements annually with clients and documenting the verification steps insurers require—well before a loss occurs.
Photo: Andrii Yalanskyi / Shutterstock
This post originally appeared on Smarter MSP.