 Stolen credentials have been around as long as email itself. This retro attack vector is making a comeback due to its low cost and simplicity.
Stolen credentials have been around as long as email itself. This retro attack vector is making a comeback due to its low cost and simplicity.
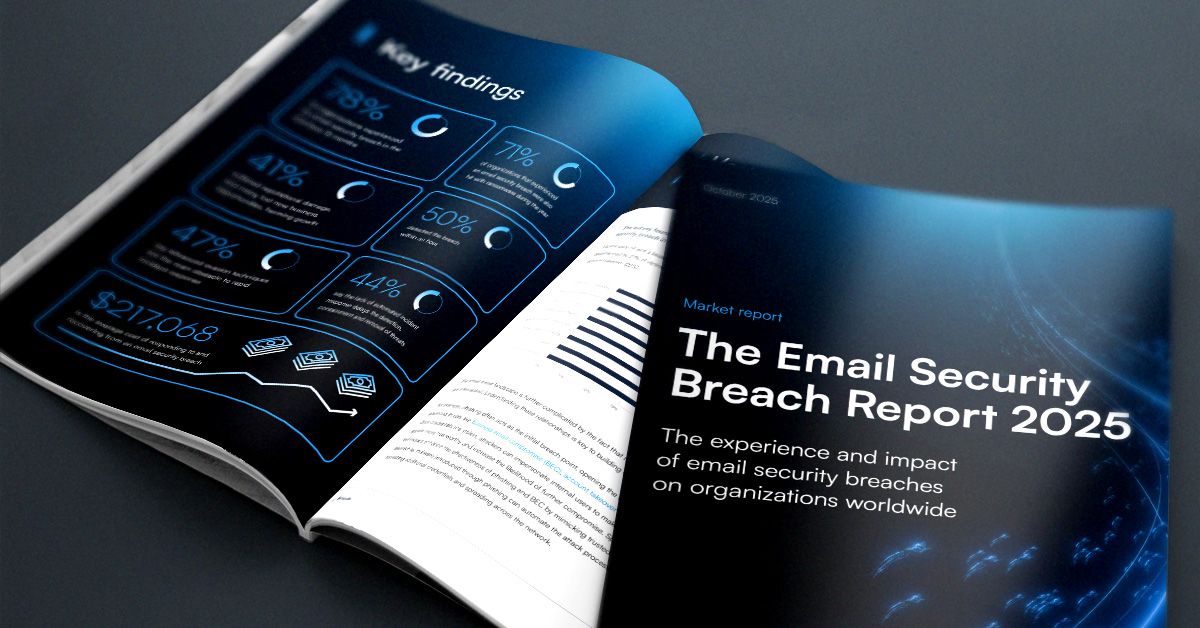
According to Barracuda’s 2025 Email Security Breach Report, credential compromise attacks are becoming both more common and more expensive. Notable findings include:
- 78 percent of organizations experienced a breach in the last 12 months
- 71 percent of those also suffered a ransomware attack within a year
- The average recovery cost exceeds $215,000, with smaller businesses impacted disproportionately
Credential compromise on the rise
These are sobering numbers for MSPs working to protect their clients’ environments.
To dig deeper into the growing problem of compromised credentials, SmarterMSP.com spoke with Dean Gefen, CEO of NukuDo, a workforce development and staffing company with deep experience in this space.
Gefen explained that compromised credentials have quietly become one of the most common entry points for cyberattacks today.
“Attackers increasingly target legitimate credentials because they allow them to blend into normal system activity, making detection much harder than traditional malware-based attacks,” Gefen said. Once inside a privileged account, attackers can move laterally, access sensitive data, and escalate privileges—often without triggering standard security alerts.
He added that organizations must distinguish credential compromise from credential abuse, where an employee misuses their access for personal gain or malicious intent. This insider risk, too, can be identified and mitigated through continuous audit controls.
Why privilege audits matter more than ever
“Regular audits of administrative privileges are essential, especially for managed service providers,” Gefen noted. MSPs often hold privileged access to multiple client environments. This means a single compromised account has the potential to affect many organizations at once.
Privilege audits help organizations understand:
- Which accounts have elevated access
- Who is using that access
- Whether those privileges are still necessary
Privileged access typically relates to admin or system accounts—Administrator, Root, DBA—and Gefen emphasized the importance of logging who used these accounts, why they accessed them, and what actions they performed.
However, he cautioned that audits alone aren’t a complete security solution. They are vital for visibility and accountability, but by nature they respond to issues rather than preventing them outright.
Gefen also shared that many organizations historically relied on password sharing, a practice now widely recognized as one of the weakest links in security. Over time, companies shifted toward credential vaulting, privilege elevation, break-glass processes, and session recording. While vaults centralize and control access, they also consolidate sensitive information—making them lucrative targets if not properly secured.
Modernizing privileged access management
Organizations and MSPs should treat privilege audits as one part of a broader access management strategy. Effective audits typically involve reviewing all privileged accounts, validating whether elevated access is still needed, enforcing role-based permissions, and removing unnecessary privileges wherever possible.
“It’s also important to monitor access patterns, track who accessed which systems and when, and enforce strict authentication and logging practices,” Gefen said.
A robust audit process should answer questions such as:
- Who has access to what?
- Why is access granted?
- How is that access provisioned?
- When should privileged access be used?
- When a privileged account is used, by whom, for what purpose, and what actions were taken?
Failing to manage privileged access can significantly expand an organization’s attack surface. If over-privileged credentials are compromised, attackers may gain immediate control over critical systems, infrastructure, and sensitive data. “For MSPs, the stakes are even higher,” Gefen added. “Trust is central to their business model. A single breach involving privileged credentials can cause data loss, operational disruption, reputational damage, regulatory issues, and ultimately, the loss of clients.”
The overlooked risk of dormant and terminated accounts
Paul Perry, practice leader of the Risk Advisory & Assurance Services Group at Warren Averett, shared another critical concern: lingering access for former employees.
Perry said the most common IT audit finding is terminated or expired employees retaining access to systems and applications. This is a gap often caused by unclear processes or responsibilities that fall outside IT and security teams.
He recommends quarterly reviews that list all individuals with access and their permission levels, with a designated owner responsible for proposing and approving changes.
Perry also highlighted the importance of least privilege, especially for small businesses: only grant access required for someone’s role, and avoid conflicting access rights. For example, accounts payable personnel should not have access to payroll.
“Administrative rights should also pass the conflict test,” Perry added. Daily system users should not also hold admin privileges, as this can complicate oversight and investigations. If an incident occurs, individuals with admin rights are typically the first scrutinized.
The bottom line for MSPs
Credential compromise may be an old tactic, but its impact today is anything but outdated. As the experts note, strong privilege management—regular audits, clear processes, and tighter access controls—remains one of the most effective ways MSPs can reduce risk. By eliminating unnecessary privileges and monitoring how accounts are used, MSPs can better protect their clients and prevent a single compromised credential from becoming a major breach.
Photo: New Africa / Shutterstock
This post originally appeared on Smarter MSP.